Updated on November 30, 2023. You can prevent credential stuffing attacks by using strong and unique passwords, enabling MFA, using a password manager, investing in a dark web monitoring tool and staying educated on emerging cyber threats. Credential stuffing often results in account takeovers – a type of identity theft in which a cybercriminal gains
Cyber insurance is a specialized insurance policy that was created to protect businesses from the losses that can occur as a result of cyber attacks. The size of your business does not matter when it comes to needing cyber insurance, and it shouldn’t be your only priority when it comes to your business’s cybersecurity. Read
Updated on April 17, 2024. Many password managers come with basic features like a built-in password generator. However, not all password managers are the same. When researching different password managers, there are other features that you should look for such as strong encryption, passkey support and 2FA code storage. Keep reading to learn the top
Deleting your LastPass account is easy and is the last step to take after finding a great LastPass alternative. There are two different processes depending on whether or not you know your LastPass master password. Please follow the steps below to delete your LastPass account. Getting Started with the LastPass Deletion Process IMPORTANT. You should export
Updated on November 30, 2023. Passwords are your first line of defense when it comes to protecting your online identity and information. To ensure the security of your accounts, you need to practice good password security. However, many people adhere to common misconceptions about password security that can put their passwords at risk of a
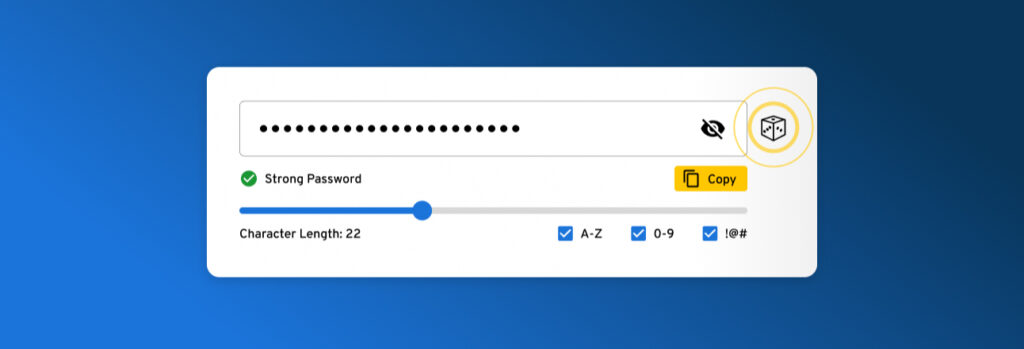
Updated on October 20, 2023. You should use a password generator to easily create strong passwords. Passwords that are short and use personal information may be easier to memorize, but this also makes them much less challenging for cybercriminals to crack. It is important to use strong passwords to protect yourself from cybercriminals Keep reading
Updated on April 18, 2024. Credentials are unique sets of attributes that identify an entity such as a person, organization, machine or service. You often use credentials to access your personal information. However, cybercriminals will use cyber attacks to steal your credentials and gain unauthorized access to your accounts. They can then steal your sensitive
As the world continues to change, so does the nature of warfare, where the Internet has become the main battleground for most of the world’s conflicts. But where is this headed? Cyber attacks have been around for much longer than you may think. The first worm was created by Bob Thomas in 1971: a malicious
The need for cybersecurity in Small and Midsize Businesses (SMBs) has never been more crucial. Any organization can suffer catastrophic effects from cyber attacks, but small businesses are particularly vulnerable. Unprepared small firms may experience tremendous financial consequences as well as damage to their reputation, productivity, staff morale and much more when a cyber attack
Revolutionizing the way businesses and consumers complete transactions, digital wallets continue to grow in popularity due to their ease of use and stronger security when compared to traditional payment methods. However, the increased use of digital wallets makes for a major target for cybercriminals. It is important to remember to follow best practices when opening
Updated on October 13, 2023 It can be hard to tell if your email has been hacked, but the most telling sign is unusual account activity such as suspicious login attempts or spam emails sent from your account. Most of us find it difficult to comprehend why somebody would hack our emails. The simplest explanation
Keeper recently released their 2022 US Password Practices Report – diving deep into the password habits of 2,000 Americans. Findings show that Americans are continuing to disregard basic password hygiene and giving in to scams, which are leaving them vulnerable to breaches and loss of money. Read on to learn more about Americans’ password habits
Keeper is your first line of protection, for yourself and your business. For businesses seeking the best cybersecurity available, Keeper’s distinctive security architecture safeguards systems and data with a simple, quick-to-deploy solution. You can feel secure about the security of your organization because of Keeper’s visibility, management, and compliance features. Keeper will guarantee the security
Updated on March 13, 2024. Remote work is a convenient style of work that allows organizations to enhance productivity and provide workers with flexibility. However, remote work comes with cybersecurity risks that can jeopardize the security of an organization. Some cybersecurity tips to remember when working from home include always using strong and unique passwords,
Updated on November 9, 2022. We live in the 21st century, where now kids are able to access the internet on their own from as early as 8 years old. Today’s youth are often called “digital natives” because they are so comfortable with living online. But as much as we may admire their proficiency with
It’s no surprise that cyber attacks are skyrocketing. Report after report indicates they’ve exploded in recent years as cybercriminals take advantage of the rapid proliferation of endpoints, growing reliance on digital devices, and shift toward remote and hybrid work. However, as the number of attacks increases, the types of attacks remain surprisingly simple. You guessed
Keeper is never at rest, continually adapting, updating and upgrading our products and services to best meet our customers’ needs, which is why we’re excited to announce two new cloud data centers in Canada and Japan. The cloud data centers are powered by Amazon Web Services (AWS) and build on Keeper’s existing global network of
Using your browser’s password manager to save the passwords for all your accounts can be tempting. Although it seems like it’s going to be the most seamless experience, it’s actually not. Browser password managers are not safe because they are not encrypted and they can be easily compromised. Read on to learn why browser password
Updated on October 18, 2023. As the holiday season fast approaches, most people turn to online shopping as a more convenient way to purchase gifts and avoid large crowds. Cybercriminals are preparing for the holidays too, but they’re doing so with bad intentions. Cybercriminals have developed easier and more advanced methods to steal consumers’ money
Stolen passwords and compromised credentials are among the leading causes of ransomware attacks. In 2021, the IC3 received 3,729 complaints identified as ransomware, with more than $49.2 million in adjusted losses. Startups and small business enterprises (SMEs) must take preventative measures to lower their risk of a ransomware attack. Keep reading to learn more about